
The FBI agent tasked with uncovering the digital footprint of Idaho mass murderer Bryan Kohberger has revealed for the first time that the killer’s calculated efforts to wipe clean his online life played a crucial role in proving his guilt.
Jeff Tanzola, a supervisory special agent in Philadelphia’s FBI field office, explained to The Independent this week how large amounts of data — text messages, Google searches, buffer logs, privacy dashboards, battery stats and usage — were missing from Kohberger’s phone and laptop, when those devices landed on his desk in 2023.
And they weren’t missing by accident.
“A lot of times when you get a phone, you get a computer, there’s a lot of evidence that just jumps off the screen at you,” Tanzola said, during a panel moderated by The Independent at the Cellebrite C2C User Summit on Wednesday. “This was not the case with that. It was the complete opposite of that.”
It appeared that Kohberger — who was arrested a month after the Nov. 13, 2022 murders of four University of Idaho students discovered stabbed to death at their off-campus home and would ultimately plead guilty in July 2025 — had attempted a digital blackout during the night of the murders.
It was one of only four periods of total inactivity, dating back to June 2022, forensic experts previously reported. But the killer’s plan backfired.

Tanzola, along with the two forensic experts he enlisted to help — Heather Barnhart, senior digital forensics expert for Cellebrite, and Jared Barnhart, the company’s head of global engagement —discovered the pattern of voids in his otherwise trackable life that appeared in the months leading up to the murders. A deeper dive then revealed some of the tracks the killer had not managed to cover.
One of the voids in his digital trail was on the night of the murders.
“He didn’t just lose signal or run out of battery,” Jared Barnhart explained. “This was an actual button press, power off, on purpose, and then a power back two hours later. And in the middle of that, four people were killed.”
The digital evidence was key to showing that the killings were premeditated, the experts have said, and bolstered the DNA evidence from a knife sheath found with the bodies, which tied Kohberger to the crime scene.
The physical evidence combined with the digital evidence created a strong case that helped form a broader picture prosecutors were prepared to present at trial. But that trial, slated for August 2025 in Boise, Idaho, would never happen.
In July 2025, Kohberger pleaded guilty and was sentenced to life in prison, avoiding the death penalty, for the murders of Kaylee Goncalves, 21, Madison Mogen, 21, Xana Kernodle, 20, and Ethan Chapin, 20. He has never explained his motive for the killings.


’Why is nothing here?’
Tanzola, who is a senior digital forensic examiner for the FBI and the lab director for the Philadelphia Regional Computer Forensic Laboratory, wasn’t called into this case initially for digital forensics, but for tactical operation.
Kohberger was located and arrested on December 30, 2022, at his parents’ home in the area of Tanzola’s operations, which is in the Poconos, Pennsylvania.
“So, ironically, I wasn’t notified initially, and remember, it was like 48 days after the event before we were able to get out there and make the arrest,” Tanzola explained. “So, a lot of time had lapsed in there.”
Months later, Tanzola was tasked with checking for evidence on Kohberger’s phone and laptop, but when he began combing through the devices, what stood out wasn’t what he found – it was what he didn’t.
And yet the pressure to find something was high.
“I’m a senior digital forensic examiner, but I wasn’t finding what I needed to find,” Tanzola said. “You’d still think you’d be able to find remnants on that phone or his computer. But that really wasn’t there. Nothing was really jumping off the screen.”
“Everyone’s looking at you. You’re the digital forensic guy. You have the phone. You’re looking at it. Why is nothing there?” Tanzola added.
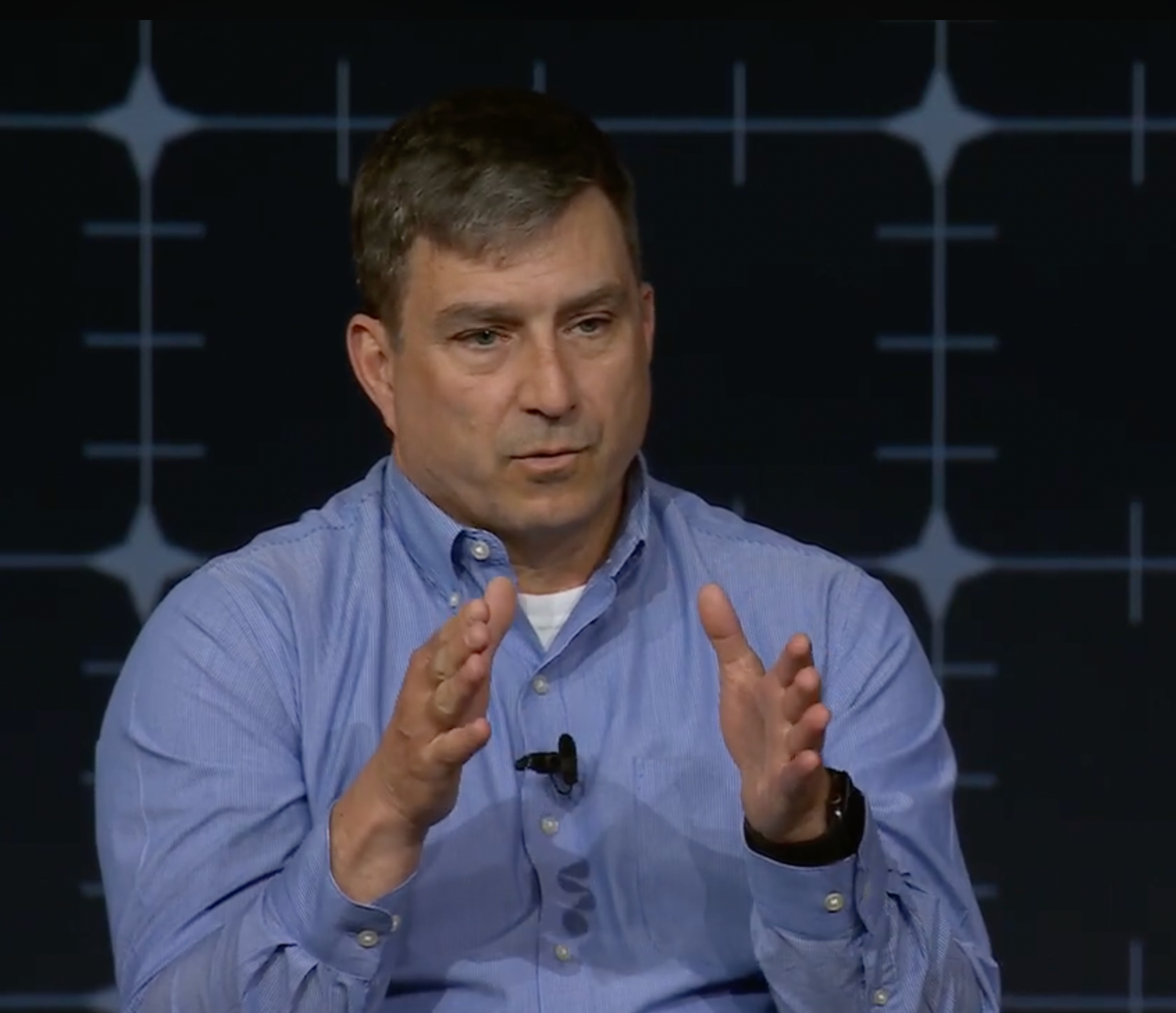
So Tanzola sought help from other FBI investigators at his lab but to no avail. “We still weren’t finding anything. So, it’s always that check and balance just to make sure you’re not missing anything.”
That next step, Tanzola said, was to reach out to Cellebrite, a digital forensics company that provides specialized software for law enforcement, government, and enterprise to unlock, extract, and analyze data.
“And that’s how we got moving. And that’s really what I want to portray for this partnership,” Tanzola said, motioning to both Heather Barnhart and Jared Barnhart, the two forensic experts on stage at the Cellebrite conference this week.
At Cellebrite’s annual conference this week, more than 900 digital forensics and investigative professionals from more than 30 countries gathered in Washington, D.C. where they discussed a wide range of criminal cases and investigative topics. Cellebrite also awarded 20 winners JUSTYS at its Digital Justice Awards.

During the panel discussion on the last night of the conference, Tanzola and the Barnharts spoke to a packed room about how the Idaho college murders case, and specifically their task of extracting any sort of evidence from Kohberger’s devices, was the most unique and difficult case they had worked on.
When asked if they had ever worked cases like this, Tanzola replied: “For me the short answer is no,” Tanzola said. “Never.”
One initial challenge was the amount of time that had passed between the murders in Moscow, Idaho, and Kohberger’s arrest, 48 days later, at his parents’ home clear across the country in Chestnuthill Township, Pennsylvania, was both a blessing and a curse.
Heather Barnhart said that so many days had passed before the phone was seized, that Kohberger had time scrub everything from his phone. But what the experts later found – was that new searches had appeared and new files saved – about the very murders he had just committed.
Searches for serial killers, porn and his victims’ murders
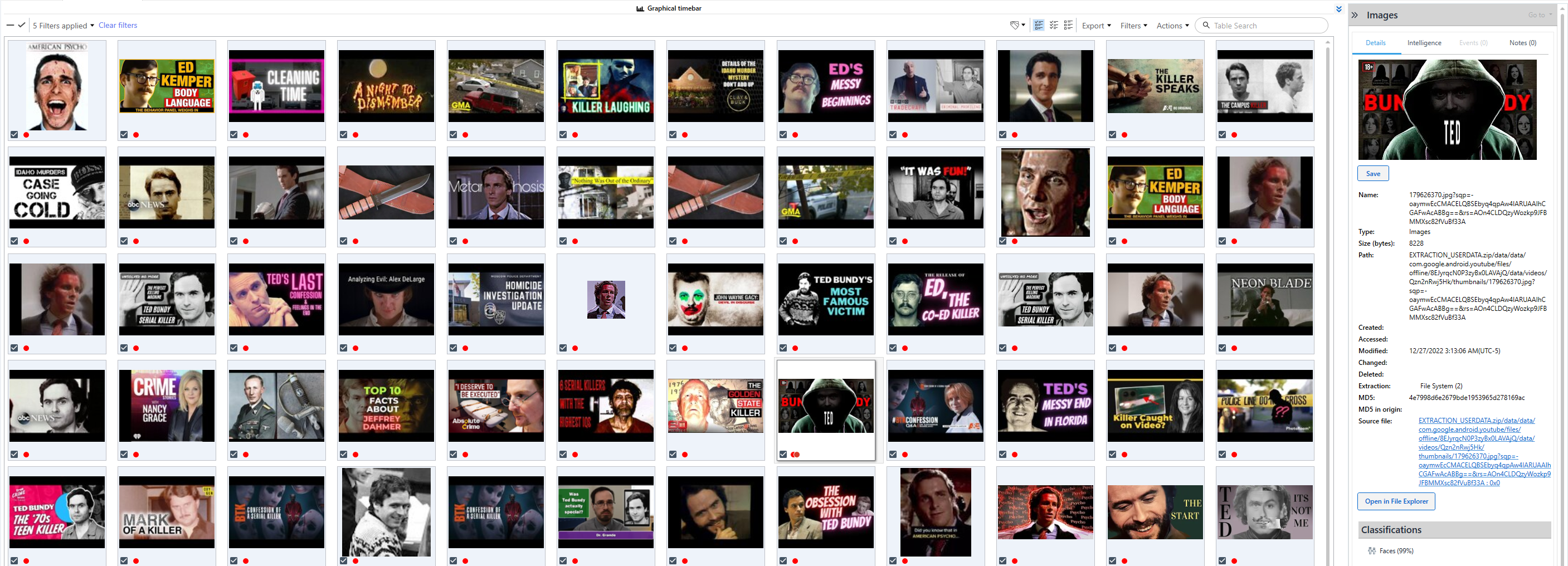
Kohberger had scrubbed his search history in the months leading up to the murders, but photos remained on his phone, and while not incriminating, many of them gave insight into who he was.
Many of the photos were selfies that showed Kohberger giving the camera a thumbs up. Some were of him posing half naked in the mirror while flexing. There was no evidence that he sent these images to anybody.
There were also saved photos of women in bikinis, though Barnharts previously confirmed that Kohberger had not taken these himself, just that “these were all cache files saved to his device.”


Kohberger succeeded in deleting a massive amount of information leading up to the murders, he was less careful in the 48 days between the killings and his arrest on December 30.
The team found that he had downloaded pdf files that included official updates on the Idaho murders case from the Moscow Police Department.
He had also downloaded PDFs and URLs of his research on serial killers.
On Christmas into December 26, 2022, just days before his arrest, Kohberger searched for more than two dozen serial killers, including Betty Lou Beets, Randy Kraft, William Lee Cody Neal, Danny Rolling, Joel Rifkin, Ted Bundy, Altemio Sanchez, Glen Rogers, Cary Stayner, John Wayne Gacy, Harvey Glatman, Paul Bernardo, Rodney Alcala, Robert Hansen, Gary Ridgeway, David Parker Ray, Cleophus Prince, Danny Rolling, Ed Kemper and Dennis “BTK” Rader.
When Moscow Police put out an alert that they were looking for a white Hyundai Elantra, on December 28, 2022, Kohberger began shopping online for a new vehicle, the experts learned.
Heather Barnhart said Kohberger’s digital trail during those 48 days proved to be a key mistake because his searches, if they had been shared with a jury, would not have supported his initial claim of innocence.
A disturbing pattern emerges
But it wasn’t a recovered message or hidden file that caused things to click for the forensic experts – it was a pattern.
The team had uncovered files scrubbed from devices, searches routed through VPNs, and URLs about serial killers he had downloaded — all of which, they say, painted a chilling picture of obsession and planning.
On Wednesday, Tanzola said it was like a flashlight aiming at the digital blackout Kohberger was attempting to create during the time of the murders.
“If you looked at it in the timeline that is is normal activity, but then see absolutely no activity for a certain time frame, obviously the timeframe around the homicide, and then there is activity again,” he said.
At 2:54 a.m. on November 13, 2022, Bryan Kohberger’s phone went dark.
The battery hadn’t died, and it wasn’t randomly powered off — it was silenced with precision. WiFi and cellular data were disabled. No location tracking on. And no background activity. A deliberate blackout during the exact window prosecutors say four University of Idaho students were brutally murdered at their off-campus home.
Two hours later, at 4:48 a.m., the phone turned back on. It would be months before investigators fully understood what that gap in activity meant.


But even defining Kohberger’s “normal” behavior proved unsettling.
“When you said normal activity… he was not normal,” Heather said. “He only had like 16 contacts.”
And those included general numbers, including AT&T, customer service, and maintenance, she added.
“So he did not have friends. He did not chat with people,” Heather added. “He had hour-long conversations with his parents. So it also felt weird on where is where is the normal.”
On December 29, a day before his arrest, Kohberger began calling and texting his parents obsessively, just as he had on the morning of the murders. If his mom didn’t answer, he’d call his dad, they said.
That same day, Kohberger searched terms like “paranoid” “psychopath” and “wiretapping.”
“It was obviously weighing on him,” Heather noted.
Complicating matters further was Kohberger’s background. As a criminology PhD student at Washington State University, Kohberger had long been immersed in the study of crime. But according to the digital forensics team, his interest crossed a line, from academic to obsessive.
“He didn’t just Google these cases,” Heather said. “He downloaded full PDFs of case files. Not once, but repeatedly. He was downloading detailed reports on serial killers,” including Danny Rolling, who also murdered college students using a similar knife.
“This wasn’t casual browsing. This was meticulous research,” she added.

To determine exactly what happened during that two-hour window on the night of the murders, the Cellebrite team re-created the digital environment and studied call logs.
“Turning off your phone isn’t enough,” Heather said. “You have to disable Wi-Fi, disable cellular, then power down. And that’s what he did.”
They discovered that in the days right before and right after the murders, Kohberger disabled WiFi access on his devices and routed his traffic through NordVPN, a tool designed to anonymize online activity.
While the act is not criminal, it is abnormal, Jared had noted.
“He was diligent in prep and cleanup and he made our job really hard,” Jared said. “This is someone who tried really hard to not be detected.”
It made it more difficult to distinguish intent from academic curiosity.
“So he had stuff on his phone that could be kind of devious, I would say, but also could be easily explainable as research for his doctoral program,” Tanzola explained.


‘What are you hiding?’
As the team continued their investigation, signs of an intensive digital cleanup emerged on Kohberger’s devices.
While the digital evidence didn’t deliver a specific “aha” moment, the team said, it painted a picture of sinister intent and a great deal of planning.
“I think it was little moments that kind of came together. His hard drive was glaringly absent. And for me, that was weird,” Heather said. “So there were so many things that just gave me doubt but I think all of that cleanup. What are you hiding?”
In a previous interview with The Independent, the Barnharts explained how the pattern of voids combined with the chilling images and searches found on a deeper dive, pointed to a well thought-out plan.
“This wasn’t someone who just snapped,” Heather said. “This was someone who planned. He didn’t accidentally stumble into this house and commit this heinous crime. It was intentional.”
“There wasn’t a single smoking gun,” Jared Barnhart added. “But we found that the digital evidence told the story of preparation.”
Despite their exhaustive efforts, the forensic team were left with many questions, something they had badly wanted to provide the grieving families.
The Cellebrite experts and Tanzola, were all slated to testify at Kohberger’s trial in August 2025 before the 30-year-old unexpectedly accepted a plea deal on June 30, 2025, avoiding the death penalty and receiving four consecutive life sentences plus an additional 10 years for burglary.
For Tanzola, the moment was bittersweet. “I think ultimately we want to see the subjects being held accountable for their crimes,” he said.
“I’m confident that he was the subject,” Tanzola added. “But you don’t know what the jury’s going to say.”


Tanzola noted that while there was pressure to find out more about the killer on his devices, a pressure to bring a solid case to trial, there was also the looming pressure of being on the stand.
“There’s also pressure with being put on the hot seat on the stand, you know, because you don’t want to be the one up there that either says something that turns the case in the wrong direction,” he said Wednesday at the conference. “Even though I’m confident that we had the evidence.”
For Tanzola, the biggest takeaway wasn’t about what was, or was not, on the phone. It was the hard work and collaboration with fellow investigators and the Cellebrite team.
“We wanted to make sure we uncovered every stone, looked at everything and made sure that we understood what the answers were,” he said. “So, I think we brought together the best case forward with the evidence that we had.”



